| Blog, Compliance, ISO 27001
Blog TrustNet in Action – ISO 27001 Compliance Made Easy TrustNet in Action – ISO 27001 Compliance Made Easy Globally regarded as an information security management standard, ISO 27001 ensures that businesses adequately safeguard their data. However, achieving...

| Compliance, ISO 27001, News
Blog How GhostWatch Simplifies ISO 27001 Compliance How GhostWatch Simplifies ISO 27001 Compliance Organizations committed to upholding strict information security management requirements must comply with ISO 27001. The guidelines for creating, putting into practice,...

| Blog, Compliance, ISO 27001
Blog The ISO 27001 Checklist for Your Business The ISO 27001 Checklist for Your Business ISO 27001, an internationally recognized standard for information security management systems (ISMS), provides a robust framework to protect your organization’s data. This...

| Blog, Compliance, ISO 27001
Blog ISO 27001 Essentials – Creating a Secure Framework ISO 27001 Essentials – Creating a Secure Framework In this digital age, information security is essential for any firm. ISO 27001 provides a comprehensive framework for managing and protecting sensitive data....
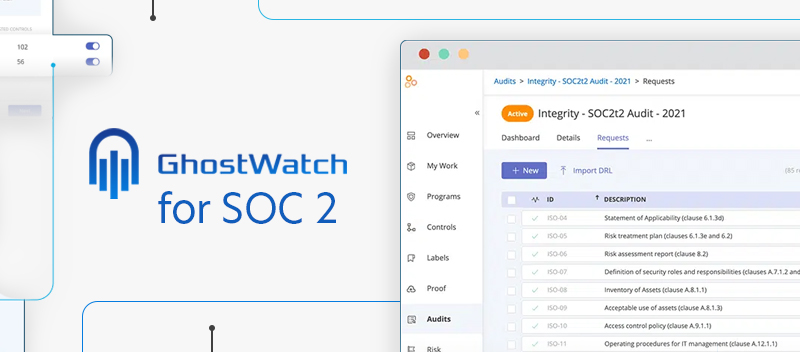
| Compliance, Managed Security, News, SOC 2
Blog How GhostWatch Elevates SOC 2 Compliance How GhostWatch Elevates SOC 2 Compliance GhostWatch by TrustNet is a global leader in security and compliance management. We are excited to delve into the benefits of GhostWatch on observing SOC 2 Compliance in this...

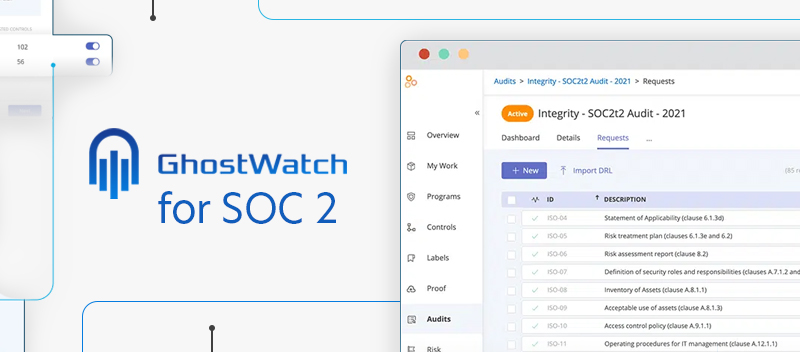
| Blog, Compliance, SOC, SOC 2
Blog Tackling Advanced SOC 2 Compliance Issues Tackling Advanced SOC 2 Compliance Issues In today’s fast-evolving world of cybersecurity, SOC 2 compliance is no walk in the park. The more companies grow and adopt new technologies, the harder it becomes for...

| Case Studies, Compliance, Information Security, Managed Security, News
Blog 2024’s Cyber Guardians: The Forefront Companies Shaping Cybersecurity Solutions 2024’s Cyber Guardians: The Forefront Companies Shaping Cybersecurity Solutions Security solutions that are proactive and adaptable are more important than ever as cyber criminals...