Does SOC 2 require data to be encrypted “at rest” or only “in transit“?

Installing strong firewalls and keeping your antivirus software up to date are excellent protections to promote an effective security posture. However, it would be best if you had other safeguards in addition to these layers of defense. Information is, for instance, particularly vulnerable to attack when it is in transit.
Therefore, it is advisable to focus on safeguarding data from endpoint to endpoint, whether “in transit” or “at rest.” End-to-end encryption scrambles all outgoing communications before the data packets leave the device, with only the target device able to make sense of it.
Section CC6 of SOC Certification, covering Logical and Physical Access, emphasizes data security and privacy and logical access to software, services, and infrastructure. The standard requires that an organization implement measures to prevent any breaches resulting from malware injection and make corrections if such breaches occur. Since hackers often take advantage of systems that are not secured, having end-to-end encryption in place is one of the best preventive strategies an organization can institute.
Encryption Requirements Found in SOC 2
Although SOC 2 standards can sometimes appear strict and intricate, they do not address encryption in any detail. There are no specific encryption requirements listed in the five Trust Services Criteria that make up the backbone of SOC 2. However, it is strongly recommended that your organization emphasize cyber hygiene as the best way to enhance its security posture.
Recommended Best Practices Based on SOC 2 Security Criteria
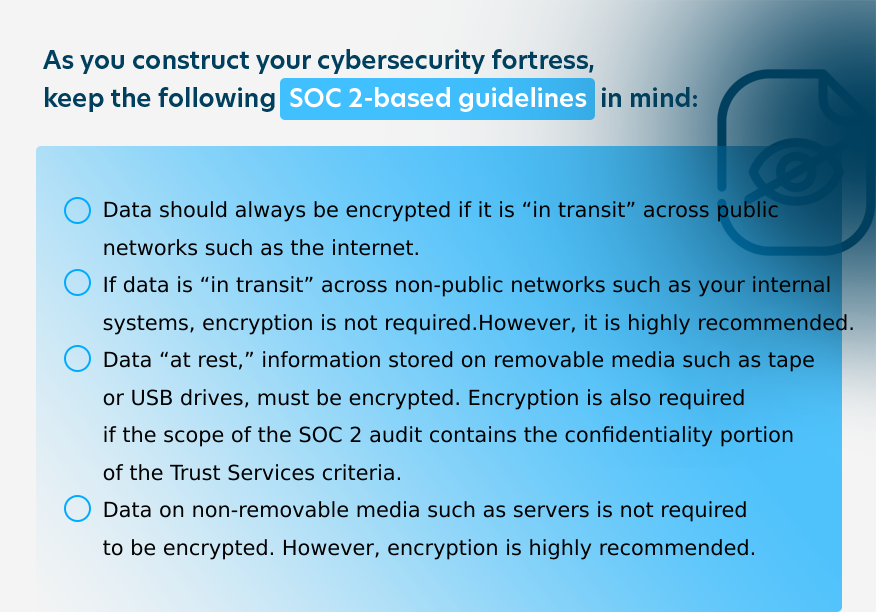
As the above recommendations suggest, your organization should always seek to encrypt all information whenever possible as the gold standard of cybersecurity.
For more on our SOC 2 compliance services, Click Here
Additional Considerations
The following recommendations are also crucial to remember, depending on the kind of information your business handles or transmits:
-
- The Health Insurance Portability and Accountability Act of 1996 (HIPAA) addresses the use and disclosure of protected health information (PHI). If the information you store or transmit is PHI under HIPAA, you should encrypt this data, whether “in transit” or at rest” unless you can demonstrate that you have put some other equally effective protective control in place.
- Any cardholder information associated with the major credit card brands (Discover, Mastercard, Visa, American Express, or JCB) is protected under the Payment Card Industry Data Security Standard (PCI DSS) and must always be encrypted, even if it is “at rest.”
- Regardless of the data type you encrypt, you should utilize cryptography based on industry-tested and accepted algorithms. The key lengths you use should provide a minimum of 112-bit key strength. Examples of suitable types are RSA — 2048 bits or higher, AES — 128 bits or higher, or TDES/TDEA — triple-length keys.
Strengthen Cybersecurity with Robust Management Practices for SOC 2 Success
In tandem with your encryption strategies, your company should create, implement, demonstrate, and regularly update a set of solid management and training practices that keep security at the forefront of your entire team’s awareness.
Implementing a thorough cyber safety and encryption policy will prepare your business to pass a SOC 2 audit with flying colors and show your clients that you are committed to end-to-end cybersecurity.