Blog
Updates on what's trending in CybersecurityUncover Security Gaps with Penetration Testing
Uncover Security Gaps with Penetration Testing

TL;DR
Penetration testing simulates real-world attacks to uncover vulnerabilities in your systems, applications, and people before attackers can exploit them. This guide explains the pen test process, its key benefits, and the types of testing every organization should consider. Plus, discover how TrustNet’s AI-powered iTrust platform enhances penetration testing with deeper risk intelligence, combining expert insight with smarter remediation for faster, stronger cybersecurity outcomes.
You’ve invested in firewalls, endpoint protection, and access controls. But how do you know they’ll hold up against a real attack?
Penetration testing puts your defenses to the test. It simulates cyberattacks in a controlled, authorized environment to identify vulnerabilities before attackers do. These simulated threats reveal how an adversary could gain access, move laterally, or exfiltrate data, and they give your team the insights needed to fix the gaps.
This approach is about understanding how exposed your systems really are, how fast your team can respond, and how prepared your organization is to handle a breach.
In this article, you’ll learn:
-
- What penetration testing is and how it differs from a vulnerability assessment
- The five core phases of a pen test
- The key benefits, types, and impact on your overall cybersecurity posture.
If you’re responsible for securing infrastructure, this guide will help you take smarter, faster action.
What is Penetration Testing?
Penetration testing is a controlled cybersecurity assessment where professionals simulate real-world attacks to uncover security weaknesses. It goes beyond surface-level scans. Pen testers actively mimic the tools, tactics, and procedures (TTPs) of malicious actors to test how your environment responds under pressure.
Unlike vulnerability assessments, which only identify known issues, penetration tests attempt to exploit those vulnerabilities. The goal is to show how attackers could chain together flaws, bypass controls, and access sensitive systems or data.
A complete pen test evaluates more than just technical configurations. It also probes human factors and internal processes. For example, testers may launch phishing campaigns or attempt social engineering to gain initial access.
Effective penetration testing helps you:
-
- Understand how attackers think and operate
- Measure the effectiveness of current security controls
- Reveal blind spots in both systems and workflows
- Prioritize fixes based on real-world risk
If you want to know how exposed your organization really is, a pen test delivers that clarity.
Ready to See Where Your Security Stands?
Our team of expert pen testers can simulate real-world attacks tailored to your environment. Get a customized penetration test that delivers actionable insights—fast.
Key Phases of Penetration Testing
A structured penetration test follows a repeatable, five-phase methodology that mirrors how real attackers operate. Understanding each phase helps your team evaluate both system resilience and incident readiness.
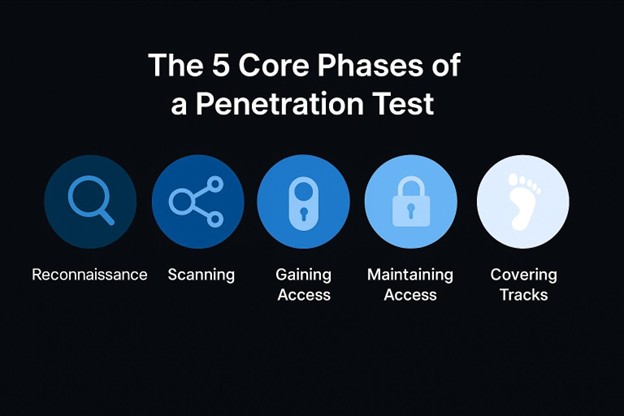
The 5 Core Phases of a Penetration Test
1. Reconnaissance
Attackers gather data on the target system using passive and active methods. This includes identifying IP ranges, DNS records, and open ports, laying the groundwork for targeted exploitation.
2. Scanning
Tools like TrustNet’s iTrust can scan for known vulnerabilities. Testers map out exposed services, outdated software versions, and misconfigured settings.
3. Gaining Access
Pen testers exploit vulnerabilities to gain control. They may use tools like Metasploit to deliver payloads, simulate brute-force attacks, or bypass authentication.
4. Maintaining Access
Simulating a persistent threat, testers escalate privileges or install backdoors. This phase evaluates how long an attacker can remain undetected in your system.
5. Covering Tracks
The tester removes evidence of the attack, clearing logs and evading detection, to mirror the behavior of advanced persistent threats (APTs).
Together, these phases form a realistic and thorough cybersecurity assessment, helping your organization detect blind spots before they can be exploited.
Benefits of Penetration Testing
Even the most well-funded security programs can have blind spots. Penetration testing helps you uncover them before threat actors do.
For IT managers and CISOs, it’s a proactive way to evaluate real-world risks. For business leaders, it delivers measurable cybersecurity improvement and peace of mind.
Here’s how your organization benefits:
— Expose Security Gaps That Matter
Identify exploitable weaknesses in networks, applications, and human workflows that traditional scans miss.
— Reduce Breach Risk with Real-World Testing
Simulate active attack scenarios to see how your systems hold up and where attackers could break through.
— Prove Compliance with Confidence
Satisfy audit requirements for PCI DSS, HIPAA, ISO 27001, and more with documented test results and remediation.
— Validate Your Defenses Under Fire
Test how well your controls actually perform when targeted by adversary-grade techniques.
— Build Trust with Stakeholders
Show customers and partners that you invest in meaningful, proactive cybersecurity measures.
Penetration testing isn’t just a checkbox; it’s a strategic move that strengthens your entire security posture.
Types of Penetration Testing
The most effective penetration tests target specific systems, behaviors, and attack vectors. Choosing the right type depends on what you need to secure.
Here are the most common types of penetration tests your organization should consider:
Network Penetration Testing
Evaluate the security of internal and external networks. Testers attempt to exploit misconfigured firewalls, exposed services, outdated protocols, and weak credentials. This test reveals how attackers could pivot through your infrastructure.
Application Penetration Testing
Examine web and mobile applications for flaws like SQL injection, cross-site scripting (XSS), broken access controls, and insecure APIs. Application pen tests help you catch vulnerabilities that directly expose customer data.
Social Engineering Tests
Simulate phishing, pretexting, and impersonation to assess how employees respond to manipulation tactics. These tests help you identify training gaps and measure your team’s resilience to real-world deception.
Each test plays a critical role in a layered defense strategy. Use them together to close the gaps that technology alone can’t cover.
Build a Security Posture That Learns and Adapts
The importance of penetration testing lies in its ability to uncover real, exploitable risks before attackers do. It’s one of the most effective ways to identify vulnerabilities early, validate your defenses, and strengthen your organization’s ability to respond.
But point-in-time testing isn’t enough in today’s dynamic threat landscape.
That’s where TrustNet’s iTrust sets a new standard. Unlike conventional approaches, iTrust merges expert-led penetration testing with AI-driven cyber risk intelligence, tailored to your risk environment.
-
- Dual-layer risk visibility: iTrust analyzes both internal and external attack surfaces, giving you a 360° view of your cyber exposure, not just what’s behind your firewall.
- Role-specific intelligence: CISOs receive real-time, high-level insights to inform strategy, and developers receive clear, prioritized remediation steps to accelerate fixes.
- Smart third-party risk management: Replace static vendor questionnaires with live, data-driven assessments that reflect real-world threats across your supply chain.
- Continuous learning engine: iTrust’s AI adapts with every scan, delivering sharper analysis and uncovering emerging risks other platforms miss.
TrustNet’s iTrust doesn’t just show you where you’re exposed. It helps you make smarter, faster, and more informed security decisions.
With iTrust, you get expert-led penetration testing powered by intelligent AI, giving you the visibility, clarity, and context to act before attackers do.
Subscribe to the TrustNet Newsletter
actionable cybersecurity strategies, and TrustNet’s cutting-edge solutions.
Data Breach: Prevent Unauthorized Access & Data Exfiltration
Data Breach: Prevent Unauthorized Access & Data Exfiltration

A data breach occurs when unauthorized individuals gain access to sensitive or confidential information. This may include personal identifiers, such as Social Security numbers and bank account details, or corporate data, such as financial records and intellectual property.
Although “data breach” and “cyberattack” are often used interchangeably, not every cyberattack results in a data breach. A breach only occurs when data is accessed without authorization.
Why Do Data Breaches Matter?
-
- Exposure of personal and corporate information to misuse.
- Financial losses, legal consequences, and reputational damage for businesses
- Identity theft, fraud, and privacy invasions for individuals
Understanding the nature of data breaches is essential in protecting critical information. By recognizing their causes and implications, businesses and individuals alike can take proactive steps to strengthen their defenses and reduce risks.
What is a Data Breach?
Data breaches can have significant consequences, especially when sensitive data is compromised. These incidents typically fall into two categories:
-
- Internal errors: Negligence or mistakes by employees, such as misplacing devices, using weak passwords, or mishandling data.
- External attacks: Cybercrminal activities, including hacking, phishing, or malware attacks., to access private data.
These incidents often lead to data exfiltration, where information is stolen and used or distributed without the owner’s consent. Regardless of the cause, a data breach represents an enormous threat to privacy, security, and trust.
Learn more about our cybersecurity and compliance services.
Common Causes of Data Breaches
— Hacking and Malware Attacks
Cybercriminals often exploit vulnerabilities using tailored hacking techniques or deploy malware to gain unauthorized access. One common tactic is phishing attacks, where victims are tricked into providing sensitive credentials or clicking on malicious links, compromising entire networks.
— Insider Threats
Employees with privileged access can sometimes become the source of data breaches. These insider threats can be intentional — such as leaking data for financial gain — or accidental, like mishandling sensitive information or falling prey to phishing schemes. Whether malicious or unintentional, insider actions pose a significant challenge to data security.
— Physical Theft
Unencrypted devices, such as laptops or external hard drives, when stolen, offer easy access to confidential data. a prevalent risk. If these devices are unencrypted, the confidential data stored within them can be easily accessed by unauthorized individuals, leading to significant data leakage.
— Misconfigurations
Misconfigurations in IT systems, such as cloud storage sets with public access or poorly implemented access controls, are another frequent cause. These errors can expose sensitive files, making them accessible to anyone who stumbles upon them — whether by accident or with intent.
Consequences of a Data Breach
Data breach consequences can be severe, creating ripple effects that impact an organization’s finances, reputation, and legal standing.
Financial Losses
Breaches can be incredibly costly. Legal fees and lawsuits from affected individuals increase these expenses. Operational disruptions, such as downtime during forensic investigations or system recovery, pile on even more costs. Financial loss from breaches can threaten the stability of any business.
Reputational Damage
A breach can tarnish an organization’s credibility almost instantly. Exposing sensitive customer data erodes trust, which can lead to clients and partners looking for safer alternatives. Rebuilding a reputation is neither quick nor guaranteed. Once the public’s faith is shaken, it casts a shadow over future growth.
Legal Implications
Falling short of compliance with established data protection laws carries legal risks that are hard to ignore. Regulations like GDPR and CCPA impose strict requirements, and failure to meet them can result in penalties, drawn-out legal battles, or enforced corrective measures. The legal impact of data breaches highlights the importance of following robust compliance practices.
The broader impact of data breaches stretches beyond immediate effects. Financial stability, trust, and legal standing can all be compromised. Mitigating these risks requires proactive planning, vigilance, and a commitment to strong data security practices.
Preventing Data Breaches
Implementing robust data security, and best practices can significantly lower the risk of data breaches.
Implement Strong Encryption
Ensure all sensitive data is encrypted both during storage and whenever it is transmitted. Encryption protects against unauthorized access, ensuring that even if someone intercepts the data, it remains unusable without the correct decryption key.
Key Details to Consider:
-
- Use strong encryption algorithms such as AES-256 (Advanced Encryption Standard with 256-bit keys), which is widely recognized as an industry standard for robust encryption.
- Prioritize proper key management by securely storing and rotating encryption keys regularly to prevent unauthorized access. Utilize tools such as Hardware Security Modules (HSMs) to protect and manage keys.
Practical Example:
A financial institution encrypts customer credit card data both in transit (e.g., during online transactions) and at rest (e.g., in database storage). Even if a database is compromised, encrypted data cannot be misused without the decryption key, which is safeguarded separately via HSMs.
Use Multi-Factor Authentication (MFA) and Role-Based Access Controls
Enhance access security through Multi-Factor Authentication (MFA), requiring users to verify their identity through additional steps, such as one-time codes or biometric verification. Pair this with Role-Based Access Controls (RBAC) to limit employee access based on job requirements.
Specific Example of MFA Implementation:
A cloud storage provider enables MFA by requiring users to log in with their password and then verify their identity through a one-time code sent via SMS or an authenticator app. This reduces the risk of unauthorized access, even if credentials are stolen through phishing.
How RBAC Works in Practice:
-
- A hospital may use RBAC to grant doctors access to patient medical records but restrict billing staff to financial data only.
- System administrators track these permissions centrally, adjusting them as roles change within the organization.
Using these approaches together minimizes the exposure of sensitive data, even during internal threats or accidental mishandling of credentials.
Keep Software Updated
Minimize security vulnerabilities by keeping all software, operating systems, and applications up to date. Unpatched software is a primary entry point for cyberattacks.
Detailed Recommendation:
-
- Automate update installations wherever possible to eliminate delays caused by human oversight.
- Run vulnerability scans after updates to confirm that systems no longer have exploitable weaknesses.
Provide Employee Training
Educate employees on detecting and addressing potential threats, as human error is one of the top causes of data breaches. Regular training fosters awareness and equips staff to safeguard sensitive information effectively.
What to Include in Training Programs:
- Phishing Simulations: Regularly test employees by sending simulated phishing emails. Provide instant feedback explaining how the scam was detected.
- Data Handling Policies: Teach employees to avoid sharing personal data over unsecured channels like public Wi-Fi.
- Incident Reporting: Ensure staff know how to identify and report suspicious activity quickly to prevent minor issues from escalating.
Nuances to Consider:
- Reinforce training periodically to ensure that employees stay current with emerging threats.
- Tailor the depth of training based on roles. For example, administrative staff should receive more detailed guidance on handling sensitive customer information compared to general staff.
By combining strong encryption, layered authentication measures, proactive software updates, and comprehensive employee training, organizations can build a multi-faceted defense against data breaches.
Protecting Your Organization Through Data Security
Understanding data breaches and their causes, as well as recognizing the importance of data security, will always be integral parts of business success. Securing your valuable assets requires building strong cybersecurity awareness throughout your organization.
Implementing breach prevention strategies, such as employee training, robust access controls, and regular audits, minimizes vulnerabilities. By staying proactive, you not only reduce risks but also create a foundation of trust and resilience to safeguard your future.
TrustNet is here to help you enhance your cybersecurity defenses. We offer tailored solutions and decades of expertise to minimize cyber risks effectively.
Take the first step towards robust cybersecurity. Contact Our Experts today.
Subscribe to the TrustNet Newsletter
actionable cybersecurity strategies, and TrustNet’s cutting-edge solutions.
The Role of Automation in Security Compliance: A Practical Guide for IT and Security Leaders
The Role of Automation in Security Compliance: A Practical Guide for IT and Security Leaders

TL;DR
Compliance with regulations like GDPR, HIPAA, and PCI DSS is increasingly complex and resource intensive. Manual methods often lead to inefficiency, errors, and scaling issues for growing enterprises. TrustNet simplifies compliance with innovative solutions like GhostWatch and the Accelerator+ approach. By leveraging Advisory, Automation, and Audits and Assessments, organizations can streamline processes, reduce operational risks, ensure continuous regulatory alignment, and save 50-70% in costs.
Managing compliance under stringent regulations like GDPR, HIPAA, and PCI DSS has become increasingly challenging. The complexity of these frameworks demands precision, yet traditional manual processes often fall short. They consume valuable resources, create bottlenecks, and leave organizations vulnerable to costly errors.
Why Manual Compliance Falls Short
-
- Time-consuming processes lead to inefficiency.
- Higher risk of human errors undermines compliance.
- Scaling becomes impractical for growing enterprises.
Automation offers a smarter approach to tackling these challenges. It streamlines procedures, ensures consistent adherence to regulations, and reduces operational risks. Organizations can simplify audits, improve ROI, and enhance efficiency across CISO compliance and IT compliance operations by implementing Compliance Automation.
This guide equips IT and security leaders with actionable strategies to successfully integrate Security Compliance automation into their workflows. Learn how to meet regulatory demands quickly and accurately while empowering your business.
Why Automation is Critical for Modern Security Compliance
Achieving cybersecurity compliance demands streamlined processes, especially as businesses face increasing complexity in compliance requirements. Security automation addresses critical challenges, such as resource strain, human error, and adapting to evolving regulations, making it an indispensable tool for modern organizations.
Mitigating Resource Drain
Manual efforts in audits, evidence collection, and compliance monitoring are time-consuming and inefficient. For instance, a tech company can spend months manually reviewing hundreds of compliance checkpoints, delaying operational goals. By automating these tasks, the same company can reduce audit preparation to a few weeks, allowing employees to focus on core responsibilities like product innovation.
Minimizing Human Error
Manual data entry and tracking lead to inevitable mistakes that compromise compliance and risk management efforts. For example, a healthcare provider may face compliance risks due to misfiled policy documents. Automation tools can correct this by securely tracking and linking evidence, ensuring no critical detail is overlooked.
Keeping Up with Regulatory Evolution
Regulatory frameworks, such as NIST or ISO 27001, are constantly updated. Remaining compliant can overwhelm teams using traditional methods. Automation ensures seamless adaptation. A financial services organization, for example, can use an automated platform to integrate the latest regulatory templates, enabling faster updates and reducing operational downtime.
Case Study: How TrustNet’s GhostWatch Helped OTS Streamline SOC 2 Compliance
Open Technology Solutions (OTS), a fintech CUSO, effectively streamlined its SOC 2 compliance process by leveraging GhostWatch’s automation capabilities. Faced with time-consuming manual tasks such as evidence collection, controls mapping, and audit preparation, OTS turned to GhostWatch’s Managed Compliance services to centralize and automate these activities. This approach reduced audit time, allowing the team to focus on strategic priorities rather than repetitive, resource-intensive tasks. The automation also minimized human error, ensured adherence to evolving SOC 2 requirements, and improved the organization’s overall compliance posture.
Explore how TrustNet’s GhostWatch can revolutionize your compliance process.
Key Components of a Successful Compliance Automation Strategy
A strong compliance management plan uses automation to increase efficiency and strengthen security. These components are essential for success:
— Policy Automation
Automation tools update security policies instantly when regulations change. For example, systems that adapt to updates like GDPR Article 30 adjust data processing records automatically. This eliminates manual errors and keeps compliance seamless.
— Continuous Monitoring
Real-time monitoring tools detect threats and track compliance across both cloud and on-premises systems. Solutions with security orchestration automation and response (SOAR) capabilities flag unauthorized activity immediately. For instance, automated alerts help organizations stop network intrusions before they escalate.
— AI-Driven Risk Assessment
AI in cybersecurity enhances risk management by predicting vulnerabilities. Generative AI simulates attacks, giving teams insight into weak points. For example, it can test system configurations to identify and prioritize the most critical risks, enabling timely action to prevent breaches.
— Unified Reporting
Unified reporting tools simplify audit preparation by consolidating compliance data. TrustNet’s GhostWatch Managed Compliance Services create audit-ready reports in minutes. For instance, businesses preparing for SOC 2 audits can quickly generate precise, detailed reports, saving significant time.
By integrating these elements, organizations use IT compliance management to reduce manual effort, enhance security, and maintain full regulatory alignment. Automation ensures lasting efficiency and resilience.
How to Implement Automation in Your Compliance Workflow
Integrating compliance automation into your workflow can save time and improve efficiency. Follow these actionable steps to transition seamlessly:
1. Assess Current Gaps
Start by identifying manual, time-consuming tasks that automation can handle better. Focus on repetitive processes like log reviews, policy updates, or access control checks, for example, instead of manually reviewing thousands of system logs, leverage compliance automation software to flag anomalies automatically. Pinpointing inefficiencies helps build a clear roadmap for improvement.
2. Choose the Right Tools
Prioritize tools that integrate easily with existing systems like SIEM (Security Information and Event Management) or IAM (Identity and Access Management). Look for features such as scalability to grow with your business and AI-driven insights for smarter decision-making. Enterprise-grade platforms, like those with enterprise compliance automation, can help you centralize and streamline processes across departments.
3. Train Teams
Automation only works when teams know how to use it. Provide targeted training on automated workflows, incident response protocols, and reporting dashboards. For instance, conduct hands-on workshops that familiarize employees with new software, ensuring they can respond confidently to alerts and maintain compliance efficiently.
4. Monitor and Optimize
Once implemented, track performance through detailed dashboards. Set benchmarks for key compliance metrics, such as response times or audit completion rates, and analyze trends. Use this data to refine processes, ensuring continual improvement and adherence to evolving standards.
A structured approach ensures your compliance automation software enhances operations, optimizes resources, and strengthens regulatory alignment across your business.
TrustNet’s Automation Solutions for IT and Security Leaders
TrustNet delivers cutting-edge technology to help organizations achieve scalable, secure, and compliant operations. Here’s how TrustNet empowers leaders with the best compliance automation tools and an innovative AI security compliance platform:
AI-Driven Compliance
TrustNet, through our innovative GhostWatch platform, leverages generative AI to predict risks, auto-generate policies, and enhance threat detection. Organizations eliminate manual errors and streamline audits using actionable, real-time insights, ensuring swift, informed decision-making.
Enterprise Scalability
TrustNet caters to complex, global infrastructures across industries like healthcare (HIPAA) and finance (PCI DSS). Our solutions simplify multi-cloud compliance and adjust seamlessly to evolving regulations, making us one of the top providers of compliance management solutions for enterprises.
CISO-Centric Features
TrustNet provides features that matter most to security leaders. From real-time risk visibility to automated reporting and audit trail generation, automated security compliance for CISOs enables proactive management and rapid response.
Cost Savings
TrustNet optimizes resources by automating labor-intensive tasks such as log monitoring and compliance tracking. Companies reduce costs by 50-70% while minimizing non-compliance risks, staying both financially and operationally ahead.
With TrustNet, IT and security leaders can access reliable, scalable tools to confidently handle today’s toughest compliance challenges.
Summary
Transform how you manage compliance with TrustNet’s innovative IT compliance software solutions. Our Accelerator+ approach equips your organization to tackle today’s most demanding challenges with precision and ease:
– Advisory
Partner with our experts to identify compliance gaps, develop tailored strategies, and safeguard your enterprise against emerging threats.
– Automation
Harness the power of GhostWatch to automate complex processes, enhance threat detection, and streamline resource allocation for peak efficiency.
– Audits and Assessments
Achieve audit success with comprehensive assessments that pinpoint weaknesses and ensure your compliance efforts stay robust.
Request a demo of TrustNet’s GhostWatch and discover how automation can pave the way for smarter, more secure operations. Connect with us today.
Subscribe to the TrustNet Newsletter
actionable cybersecurity strategies, and TrustNet’s cutting-edge solutions.
Cybersecurity Awareness: Training to Prevent Human Error
Cybersecurity Awareness: Training to Prevent Human Error

TL;DR
Human error caused 95% of breaches in 2024. Cybersecurity awareness training teaches employees to recognize threats, reduce risky behaviors, and respond quickly. This guide covers what awareness means, how to implement it, and why TrustNet’s training platform is the all-in-one solution to build a security-first workforce.
Human error contributed to 95% of data breaches in 2024, driven by insider threats, credential misuse, and user-driven errors, according to a new study by Mimecast. This statistic only means that without proper training, people become the weakest link. But with the right guidance, they can be your strongest defense line.
Cybersecurity awareness is the foundation of a strong digital defense. It refers to educating individuals, especially employees, on recognizing threats, understanding risks, and taking informed actions to prevent breaches.
In this article, you’ll learn:
-
- What cybersecurity awareness is and why it matters
- The core components of effective employee security training
- Practical steps for building a proactive, security-conscious culture
Let’s dive into how cybersecurity training can turn awareness into action and risk into resilience.
What is Cybersecurity Awareness?
Cybersecurity awareness means understanding the risks, threats, and safe practices that help individuals protect digital systems and data. It’s more than knowing that cyberattacks exist; it’s about recognizing how and why they happen and what actions prevent them.
Organizations use employee security training and cyber risk education to help teams develop this understanding. Cybersecurity awareness empowers people to make smarter decisions in real time, whether they’re opening emails, using corporate networks, or handling sensitive customer information.
At its core, cybersecurity awareness teaches employees to:
-
- Identify common threats, such as phishing, malware, and social engineering tactics
- Understand their responsibility in safeguarding systems and data
- Apply security best practices, like using strong passwords and reporting suspicious activity
- Minimize risky behaviors that attackers often exploit
This awareness turns each team member into a human firewall. When people understand the risks and take ownership of their role, organizations drastically lower the chance of breaches caused by everyday mistakes.
Ready to Turn Awareness Into Action? TrustNet’s cybersecurity awareness training programs are designed with expert-led modules, real-world simulations, and continuous learning tracks to equip your team with the tools they need to spot threats and stop them.
Key Components of Cybersecurity Awareness Training
Effective cybersecurity awareness training programs focus on practical knowledge and real-world scenarios. The best programs don’t just inform—they change behavior. Below are the core cybersecurity training components every organization should implement:
1. Phishing Simulations
Phishing remains one of the most common entry points for cyberattacks. Simulated phishing exercises train employees to:
-
- Spot suspicious emails and malicious links
- Recognize spoofed sender addresses and urgent language
- Think critically before clicking or sharing information
These simulations build real-world instincts that reduce risk.
2. Password Security
Weak or reused passwords give attackers easy access. Training should cover:
-
- How to create strong, unique passwords
- The importance of using password managers
- How and why to enable multi-factor authentication (MFA)
Reinforcing these basics helps close critical security gaps.
3. Social Engineering Awareness
Attackers often manipulate people, not just systems. Employees must learn to:
-
- Identify emotional triggers and persuasion tactics
- Verify identities before sharing sensitive information
- Stay alert to pretexting and impersonation attempts
Understanding the psychology behind attacks improves defense.
4. Incident Reporting
Quick reporting limits damage. Training should encourage employees to:
-
- Report suspicious activity immediately
- Know where and how to report incidents
- Understand that reporting isn’t optional; it’s essential
When employees act fast, organizations respond faster.
Each of these components strengthens your workforce against evolving threats. When combined, they form the backbone of a proactive security culture.
Benefits of Cybersecurity Awareness Training
The benefits of cybersecurity awareness go far beyond individual knowledge—they directly strengthen your organization’s ability to detect and prevent threats. Here’s how effective training delivers results:
1. Reduces Human Error
Human mistakes cause the majority of cyber incidents. Training helps employees:
-
- Avoid risky behaviors like clicking suspicious links or sharing credentials
- Understand how small actions impact broader security
- React quickly and correctly when faced with threats
Reducing human error directly lowers the chance of breaches.
2. Improves Security Culture
Awareness creates accountability. When employees take ownership of security:
-
- They stay alert to signs of phishing and social engineering
- They adopt safe practices as part of their daily work routines
- Security becomes a shared responsibility, not just IT’s job
A strong culture makes security second nature.
3. Helps Prevent Data Breaches
Trained teams make fewer costly mistakes. As a result:
-
- Sensitive data stays protected
- Attackers find fewer vulnerabilities to exploit
- Incident response becomes faster and more effective
Prevention always costs less than recovery.
4. Supports Regulatory Compliance
Frameworks like GDPR, CCPA, and HIPAA require organizations to protect data through proper training. Cybersecurity awareness programs:
-
- Align with legal obligations
- Reduce the risk of fines and investigations
- Demonstrate due diligence to auditors and regulators
Compliance isn’t just a box to check, it’s a defense strategy.
When you invest in training, you empower your team to take action that reduces cyber risks every day.
How to Implement Effective Cybersecurity Awareness Programs

Here’s how to implement cybersecurity awareness that sticks:
1. Use Engaging Methods
Traditional slide decks don’t change behavior. Use interactive training methods like:
-
- Gamified learning modules
- Realistic phishing simulations
- Scenario-based role-playing
Engagement boosts retention and helps employees respond confidently in real-world situations.
2. Conduct Regular Refreshers
Cyber threats constantly evolve. Your training should too. Build continuous learning programs that include:
-
- Quarterly knowledge refreshers
- Monthly security bulletins
- Just-in-time microlearning after incidents
Reinforcing knowledge over time keeps it top of mind.
3. Measure Effectiveness
Training without metrics misses the mark. Track performance through:
-
- Pre-training/post-training assessments
- Simulated phishing click rates
- Reporting and response rates
Use results to improve and personalize future training.
When you combine engaging content, regular updates, and data-driven improvements, your team becomes your strongest security asset.
Build a Workforce That Actively Defends Your Business
Human error drives the majority of security breaches, but with the right training, teams can recognize threats early and respond with confidence. If you want to prevent human error breaches and reduce cyber risks, you need more than occasional reminders — you need a system.
That system should be more than standalone training sessions. Effective security awareness training must be integrated into a broader Governance, Risk, and Compliance (GRC) strategy, ensuring that risk mitigation is not just reactive but proactive and continuous. By embedding awareness into your GRC framework, you create a culture of accountability and informed decision-making that aligns with organizational policies and regulatory requirements.
TrustNet’s Enterprise Awareness Training Platform delivers exactly that:
-
- User Training: Interactive content that goes beyond theory; videos, games, simulations, and real-world scenarios
- User Phishing: Automated phishing, vishing, and smishing drills using thousands of customizable templates
- Reporting: Executive-ready dashboards and detailed analytics to track progress and prove impact
TrustNet helps you turn awareness into action, and people into your first line of defense. Connect with us today.
Subscribe to the TrustNet Newsletter
actionable cybersecurity strategies, and TrustNet’s cutting-edge solutions.
TrustNet Trending
Register for TrustNet’s bi-Weekly cybersecurity newsletter
Webinars
Valuable information on IT security and complianceCyber Supply-Chain Attacks
Should we be Afraid of our Third Party Vendors? The biggest threat in cybersecurity might be under our noses. According to a recent Ponemon Institute study, US organizations are failing to assess the risk of attacks and data breaches from vendors in their supply...
Cyber Pearl Harbor – United States Military Preparedness and Lessons Learned For Business
December 7, 2016 marks 75 years since the Japanese surprise attack on Pearl Harbor. Today, by most estimates, as much as 85 percent of US critical infrastructure is owned by the private sector. The government's senior-most civilian, military, and intelligence...
Hacking the Human – How Social Engineering Owns Our Users
Highly targeted Social Engineering attacks are wreaking havoc in cybersecurity. In one recent incident, hackers used Social Engineering to defraud a US company out of nearly $100 million. The increased use of these techniques is directly related to the fact that they...
Incident Response – Anatomy of a Cybersecurity Breach
Ever wonder what it's really like to be inside a cybersecurity breach? The increasing number of high-profile compromises are a valuable warning for cybersecurity professionals. A real-life incident shouldn't be your first. Join our panel of cybersecurity experts as we...
RSA Conference 2016 – Seven Key Takeaways You Can Use Today
RSA Conference 2016 broke new ground as the largest gathering of security professionals with +40,000 attendees, +500 exhibitors, and +213,000 square feet of exhibit space. While keynotes, and many speakers addressed global and national issues, these topics often have...
Smackdown: Wrestling with Security and Compliance in the Cloud
Rapidly evolving cloud technologies makes evaluating security and compliance risks a difficult proposition. Cloud service providers and their clients have a shared responsibility for security and compliance; but defining these roles can keep you running in circles. In...
How to Survive the Top Ten Cybersecurity Risks of 2016
2016 looks like another challenging year for cybersecurity. Security threats are multiplying all over the globe and threaten to disrupt businesses, government, and individuals. Join our panel of cybersecurity experts as we discuss predictions for the Top 10...
Payment Card Industry Security and Compliance Round Table
Join InfraGard Atlanta and our panel of experts discussing the latest PCI trends and challenges. Our panel includes representatives from Northwestern University, Comodo, and TrustNet. Three organizations, with three very different perspectives. We'll dive into a...
You’ve been hacked. Now it’s time for “Plan B”
With global Cybercrime costs soaring to $445 billion a year, Cyber Insurance is one of the hottest trends in risk mitigation. Join industry experts from TrustNet and Cyber Data Risk Managers LLC for a dynamic and interactive discussion about Cyber Insurance. Whether...
How the Retail Industry is Shaping the Future of Cybersecurity
An estimated two-thirds of the U.S. gross domestic product comes from the retail industry. This activity has also driven the mass accumulation of payment card data that now serves as a de facto currency. The unfortunate consequence is that criminals can be more...
Conquering our Biggest Security Challenges in 2015
This webinar features industry cybersecurity experts discussing how they are addressing their biggest security challenges and what's keeping them up at night. We'll get practical advice on how they use tools, technologies, and processes to protect their enterprises....
Whitepapers
In-Depth knowledge and reports on cybersecurity's most common questionsNavigating Compliance: PCI DSS v4.0.1 and Beyond
TL;DR PCI DSS v4.0.1 is now the definitive security standard for any organization that handles cardholder data. With enforcement starting March 31, 2025, this whitepaper breaks down key changes, including risk-based controls, stricter MFA rules, and scope validation,...
Ethical Hacking vs. Penetration Testing: Key Differences, Applications, and Best Practices Every Security Professional Should Know
I. Introduction The digital age has unlocked immense opportunities but also presented major risks. Cyber-attacks are escalating in frequency and complexity, targeting sensitive data, operations, and infrastructure. For businesses and individuals, proactive...
PCI DSS 4.0: Updated Password Requirements and Compliance Audit Insights
PCI DSS 4.0 represents a major update, with enhanced security measures to reinforce compliance and mitigate risks for organizations processing, storing, or transmitting payment data. A key focal point of this update is the refinement of password requirements, which...
NIST Cybersecurity Framework: A Comprehensive Guide to CSF Tiers and Implementation
Modern businesses constantly face an avalanche of cyber-attacks from increasingly sophisticated elements. At the same time, they also have to adhere to stringent compliance standards while safeguarding sensitive information. Such a situation can be handled...
Vendor Management KPIs: Essential Metrics for Effective Third-Party Risk Control
Across all industries, managing vendors is now essential to corporate success. Managing these partnerships is essential for businesses that depend on suppliers for specific services. However, vendor relationships also bring inherent risks – regulatory compliance...
iTrust: A Tool for Today’s Cybersecurity Challenges
Blog Organizations worldwide are grappling with safeguarding their digital assets against escalating threats. These threats encompass traditional cyber-attacks and include more insidious risks that lurk within the vast amounts of data organizations generate...
Understanding CCPA: A Comprehensive Guide for Businesses
Blog The California Consumer Privacy Act (CCPA) is a landmark law that has reshaped the landscape of consumer privacy rights in the United States. The CCPA represents a pivotal shift in the balance of power between consumers and businesses regarding data...
Beyond the Audit: Proactive SOC 2 Compliance Strategies for 2024
Blog As we navigate through 2024, the importance of SOC 2 or Systems and Organizations Controls 2 in maintaining data security and privacy continues to surge. With escalating cybersecurity threats, businesses are tasked with protecting their sensitive data...
Here’s Why Top Organizations Obsess about GRC and Why You Should Too
Best practices help companies operate more efficiently, maintain quality standards, and minimize exposure to risks. These are possible because industry best practices evolve in response to real-world challenges. The adaptive methods and preventive measures they...